Information
Work at the computer. How to avoid occupational diseases?
 They came without an invitation and said: “Hello, allow me to introduce myself: these are we, three new diseases of the new century, -“ text neck ”,“ smartphone finger ”and“ dry eye ”. However, we, educated people who are knowledgeable in the rules of etiquette, do not want to answer them “very nice” and “welcome”.
They came without an invitation and said: “Hello, allow me to introduce myself: these are we, three new diseases of the new century, -“ text neck ”,“ smartphone finger ”and“ dry eye ”. However, we, educated people who are knowledgeable in the rules of etiquette, do not want to answer them “very nice” and “welcome”.
Even judging only by the names of these diseases (in the foreign press, respectively, “text neck”, “smartphone finger”, “dry eye”), there is a feeling that we are talking about some sort of gang warfare. In fact, it is: these near-computer diseases are fighting against us, the near-computer population, fighting on all fronts. Not so long ago, electronic gadgets have come into our lives, and already more than 80% of white-collar workers in all developed countries suffer from symptoms of these diseases. In 2011, scientists from the British Physiotherapy Continue reading
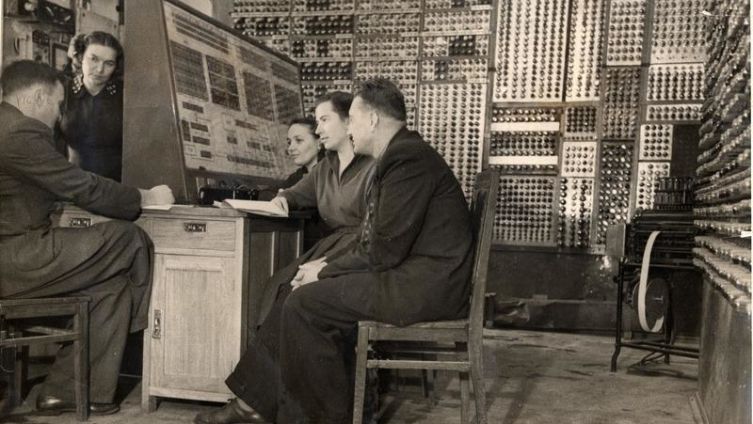
What is the Morris Worm?
 In early November 1988, the first ever network attack on computers connected to the global network took place. Her culprit was Cornell University graduate student Robert Tappan Morris.
In early November 1988, the first ever network attack on computers connected to the global network took place. Her culprit was Cornell University graduate student Robert Tappan Morris.
The program, written by Robert Morris, had a small dictionary of the most well-known passwords, which provided it with penetration of 10 percent of computers connected to ARPANET. Once on a foreign computer, the program first checked whether the same program was already installed here. If the computer was still “clean”, the program masked its presence in the system, read a file that contained information about users of the “occupied” system, forwarded this information to the author, and then Continue reading
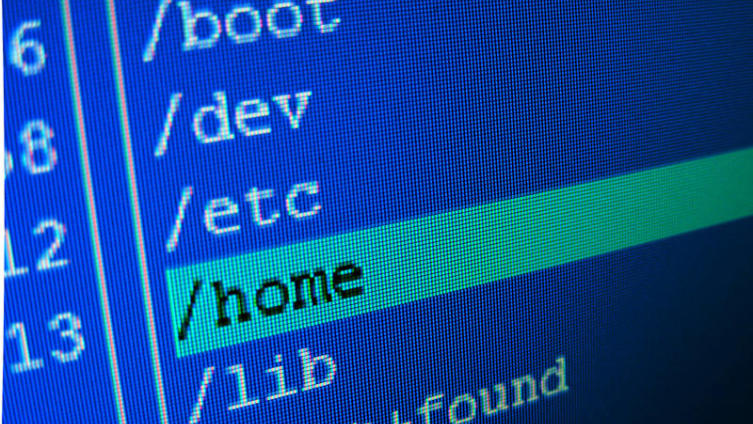
How to keep your computer healthy?
 A computer is a universal tool that allows you to work, relax, chat, or shop. At the same time, even without visiting malicious sites, you cannot be sure of protecting your computer, as the search for vulnerabilities in the IT industry is always ahead of the development of protection. Thus, you should independently worry about the safety of your data with the help of an antivirus.
A computer is a universal tool that allows you to work, relax, chat, or shop. At the same time, even without visiting malicious sites, you cannot be sure of protecting your computer, as the search for vulnerabilities in the IT industry is always ahead of the development of protection. Thus, you should independently worry about the safety of your data with the help of an antivirus.
What is it and why is it necessary? The comfort of using a particular system is inversely related to security. This rule has some derogations, but in general terms it looks just like that. Therefore, no matter how comfortable it is to work, one must assume the possibility of hacking. Even by accessing regular pages and not clicking any unnecessary links, you can get malware onto your computer if the page you Continue reading