monitors
Computer graphics. What is it?
 Speaking in a dry scientific language, computer graphics (for brevity we will call it CG, in the colloquial terms of users – CJ) refers to the field of computer science, which studies methods and means of creating and processing images using hardware and software systems.
Speaking in a dry scientific language, computer graphics (for brevity we will call it CG, in the colloquial terms of users – CJ) refers to the field of computer science, which studies methods and means of creating and processing images using hardware and software systems.
This is read by a person who is far from such high matters, understands little, is frightened and involuntarily makes himself negative about her. But there is nothing to be afraid of. CG for us now is the second environment after the environment of nature, which many have ceased to see, sitting in the city walls and facing the monitor. If translated into a very simple language, then CG are those images that we see on this very monitor or screen and which are easy to copy, for example, onto paper, which has still remained one of the external storage media. Continue reading
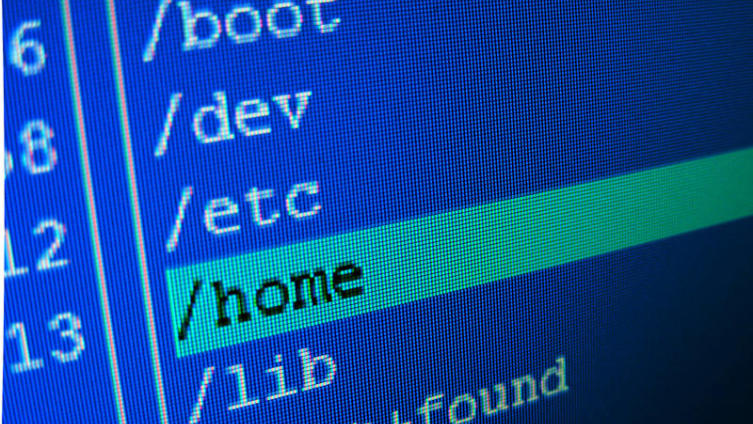
Can I start programming in 5 minutes? Is quite real
 The topic of programming lessons has been raised more than once, but many of these materials are either too complicated for beginners or require additional preparation and installation of various (often expensive and time-consuming) software packages. Is it possible to do without all this? Can!
The topic of programming lessons has been raised more than once, but many of these materials are either too complicated for beginners or require additional preparation and installation of various (often expensive and time-consuming) software packages. Is it possible to do without all this? Can!
We will try to get by with a minimum of additional information, so that in 5 minutes our first program will work. So let’s get started. Introduction According to the encyclopedia, a computer program is a sequence of instructions for a computer. A programming language is a formalized way of writing computer programs. It is important to note that the computer itself does not need a “human” language; it copes well with machine codes in binary format. These codes are simple instructions like: “Take the number at address 100, add the number at address 101, put the result in cell 102”. Continue reading
What is the Morris Worm?
 In early November 1988, the first ever network attack on computers connected to the global network took place. Her culprit was Cornell University graduate student Robert Tappan Morris.
In early November 1988, the first ever network attack on computers connected to the global network took place. Her culprit was Cornell University graduate student Robert Tappan Morris.
The program, written by Robert Morris, had a small dictionary of the most well-known passwords, which provided it with penetration of 10 percent of computers connected to ARPANET. Once on a foreign computer, the program first checked whether the same program was already installed here. If the computer was still “clean”, the program masked its presence in the system, read a file that contained information about users of the “occupied” system, forwarded this information to the author, and then Continue reading